Keeping your IT and computer systems protected against harmful elements should be a priority for all businesses. Because the systems are integral to many business dealings, you should be mindful of where and how you house them. Simple things, such as temperature and humidity changes, can damage the delicate components of your equipment. Take CRAC, or Computer Room Air Conditioning, for example.
Computers need to stay in low levels of humidity and heat to function normally. Any changes to this environment can destroy electronic equipment. Another culprit to watch out for is moisture. What you need to combat water from damaging delicate wiring is a water leak detection system.
Water leaks can spring from anywhere, especially if the data centre is located near water sources. Thankfully, you have many tools at your disposal to detect water leakage and act quickly.
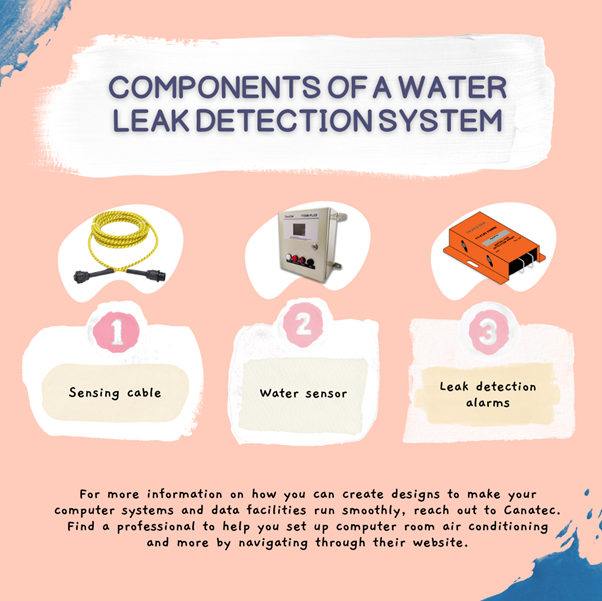
1) Sensing cable
High-tech sensing cables are best for helping you determine water leakage near the bottom of your data facility. Some of them can even detect the source of the water leak and lead you directly to it. You may want to invest in advanced sensing cables.
2) Water sensor
These are your first line of defence against water. Water sensors help you determine whether moisture is present in the air or the ground. Pay attention to them to know more about the leak.
3) Leak detection alarms
Tracetek and other systems have built-in alarms with their sensors to quickly notify you when your electronics are in danger. You can solve the problem before they irreparably damage computer components with leak detection alarms.
For more information on how you can create designs to make your computer systems and data facilities run smoothly, reach out to Canatec. Find a professional to help you set up computer room air conditioning and more by navigating through their website.



